About us
FileQRTrans is a web-based application that uses Rivest-Shamir-Adleman Encryption designed and implemented by TechTitans. The system provides a safe and user-friendly file sharing environment and secured by the RSA encryption algorithm to avoid unauthorized access and data replication on shared files.
Rivest-Shamir-Adleman (RSA) Encryption
Rivest-Shamir-Adleman (RSA) is a public-key cryptosystem, one of the oldest widely used for secure data transmission. The initialism "RSA" comes from the surnames of Ron Rivest, Adi Shamir and Leonard Adleman, who publicly described the algorithm in 1977. An equivalent system was developed secretly in 1973 at Government Communications Headquarters (GCHQ), the British signals intelligence agency, by the English mathematician Clifford Cocks. That system was declassified in 1997.
In a public-key cryptosystem, the encryption key is public and distinct from the decryption key, which is kept secret (private). An RSA user creates and publishes a public key based on two large prime numbers, along with an auxiliary value. The prime numbers are kept secret. Messages can be encrypted by anyone, via the public key, but can only be decrypted by someone who knows the private key.
The security of RSA relies on the practical difficulty of factoring the product of two large prime numbers, the "factoring problem". Breaking RSA encryption is known as the RSA problem. Whether it is as difficult as the factoring problem is an open question. There are no published methods to defeat the system if a large enough key is used.
RSA is a relatively slow algorithm. Because of this, it is not commonly used to directly encrypt user data. More often, RSA is used to transmit shared keys for symmetric-key cryptography, which are then used for bulk encryption–decryption.
How the System works
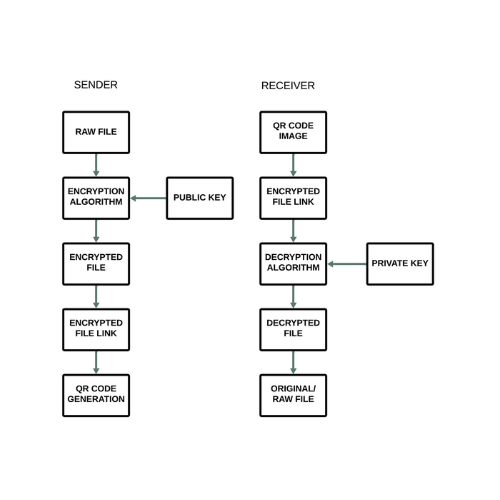
The system provides two functions, both for sender and receiver and uses different keys for encryption and decryption or public key encryption. Public key encryption is a method of encrypting or signing data with two different keys and making one of the keys, the public key, available for anyone to use. The other key is known as the private key. Data encrypted with the public key can only be decrypted with the private key. As it needed two different key for each function, the system provides a more secure way for data file transmission through internet and avoid the exploitation from the interceptor.